AWS Systems Manager (SSM) allows you to manage your Amazon Web Services resources easily and securely, without the burden of complex infrastructure. In this article, discover how AWS Systems Manager Session Manager allows Cyberwatch to access your cloud assets quickly and securely, without additional deployment, to simplify vulnerability management.
What is AWS Session Manager?
Session Manager is a feature of AWS Systems Manager that allows you to open secure sessions on EC2 instances without the need for SSH or RDP/WinRM access.
Session Manager eliminates the need to open SSH or RDP/WinRM ports, enhancing security.
Cyberwatch allows you to configure agentless connections via AWS Session Manager.
Configuration steps on AWS
On the AWS side, you need to configure EC2 to allow Session Manager. Your user must also have the necessary permissions to use Session Manager on your EC2 and execute commands on it.
1. EC2 configuration
1/ Verify that the SSM agent is installed on your EC2 instance:
The SSM agent is installed by default on certain images provided by AWS or trusted providers.
If your image does not include it, you will need to install it manually by following the AWS documentation.
To verify that it is installed on your instance, you can follow the steps provided by AWS.
2/ Create the IAM role for EC2:
- Go to the AWS IAM console and create a role.
- Select “AWS Service” as the approved identity type, then choose “EC2” as the service or use case.
- In step 2, choose the “AmazonSSMManagedInstanceCore” policy provided by AWS.
- In step 3, give the role a name (for example: Cyberwatch-EC2-SSM) and create it.
3/ Attach the IAM role to the EC2 instance:
- Go to the details page for your EC2 instance.
- In the “Actions → Security → Change IAM Role” tab, select the role you just created.
2. Configuring permissions for the user
1/ Go to the AWS IAM console and create the following policy in JSON format (in “AWS IAM → Policies → Create Policy”):
{
‘Version’: “2012-10-17”,
“Statement”: [
{
“Effect”: “Allow”,
“Action”: [
“ssm:DescribeInstanceInformation”,
“ssm:SendCommand”,
“ssm:GetCommandInvocation”
],
‘Resource’: “*”
}
]
}This policy allows Cyberwatch to interact with AWS Session Manager to execute commands on your EC2 instances. However, it does not allow access to Session Manager via the AWS interface.
2/ Associate this policy with your user.
Once these steps are complete, you can use AWS Session Manager as a connector to scan your EC2 instances in Cyberwatch.
3. Configuration steps on Cyberwatch
Now that your AWS environment is ready, you need to configure Cyberwatch to use AWS Session Manager as a connector and scan your EC2 instances. Here are the steps to follow:
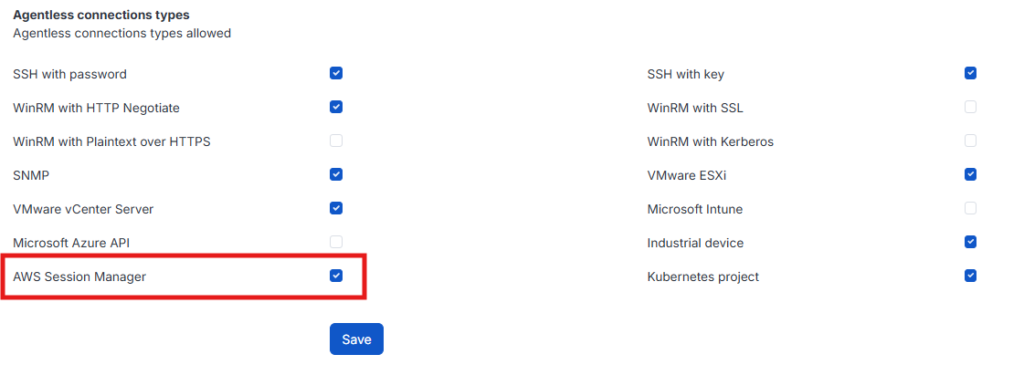
1/ Enable the AWS Session Manager connector:
By default, the AWS Session Manager connector is disabled. To enable it: go to “Administration →Connector Management” and enable “AWS Session Manager” in “Agentless Connection Types”:
2/ Add your asset:
- Go to “Asset Management → Agentless Connections.”
- Click “Add” to create a new connection.
- Fill in the required fields (name, AWS credentials, etc.).
- Validate the connection and run a scan to test it.
Here is an example:
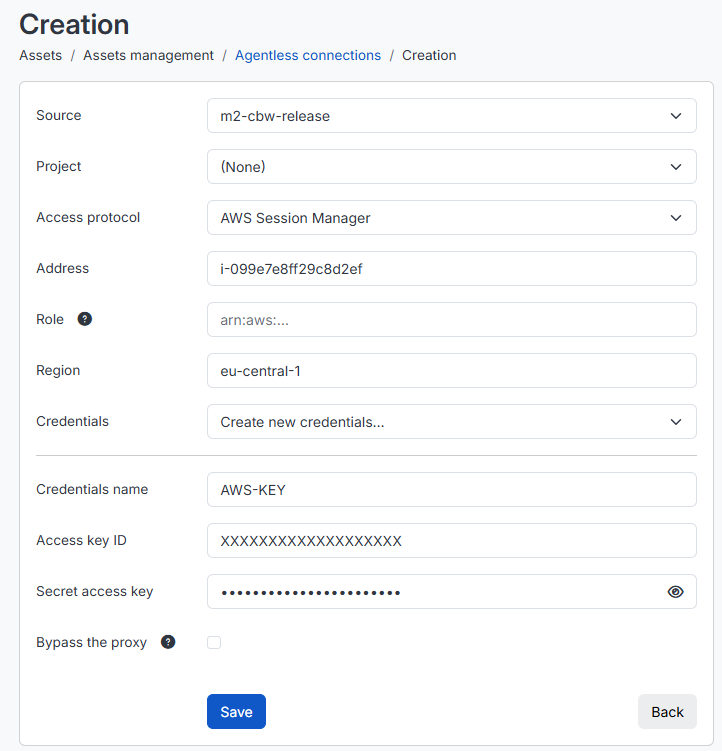
AWS connection keys can be created from the AWS interface by clicking on the account name in the top right corner, then “My Security Credentials.”
Once these steps are complete, you will be able to view the scan results and monitor your assets continuously. To go further, consider configuring an “Amazon Web Services” discovery to automatically add multiple assets.