Do you think you can control your cybersecurity by monitoring your internal infrastructure? It’s a good start, but it’s far from enough!
According to a recent study, around 79% of cyber risks lie outside your internal IT perimeter, particularly on the internet (cloud services, exposed APIs, outsourced infrastructure, etc.).
This is a massive blind spot that continues to grow, representing just as many potential entry points for cybercriminals.
So how can you regain control? This is the challenge addressed by EASM (External Attack Surface Management).
Find out what it consists of, why it has become essential, and how Cyberwatch helps you map, analyze, and monitor your external attack surface.
What is External Attack Surface Management (EASM)?
Definition and key principles
EASM is a cybersecurity approach that involves continuously identifying, analyzing, and monitoring all of an organization’s digital assets exposed on the internet in order to secure them before a potential malicious actor exploits them.
The principle is simple: adopt the attacker’s point of view.
In concrete terms, this involves scanning the internet to detect everything that is visible and accessible on behalf of your organization: misconfigured servers, expired certificates, open APIs, etc., and then proactively correcting these vulnerabilities.
What does an organization’s external attack surface cover?
The external attack surface corresponds to all the digital exposure points through which your organization is visible (and potentially attackable) from the Internet. These include:
- Domains and subdomains: institutional websites, customer portals, extranets, test environments, pre-production environments, marketing microsites, domains that have been purchased or abandoned but are still active, etc.
- Exposed servers and infrastructure: web servers, VPNs, remote access gateways, bastions, security appliances, etc.
- Cloud services and outsourced environments: cloud instances, public storage, misconfigured SaaS services, exposed buckets, IaaS or PaaS environments open by default, etc.
- APIs and application services: public APIs, unauthenticated endpoints, business services exposed for partner or mobile integrations, etc.
- Accessible network ports and services: obsolete protocols, unnecessary services left open, exposed administration interfaces, etc.
- Certificates, identities, and technical dependencies: expired, misconfigured, or compromised certificates, vulnerable software dependencies, unmaintained technical components, etc.
The external attack surface therefore encompasses a multitude of assets, often scattered, sometimes poorly documented, and frequently overlooked.
Why EASM is essential in organizations’ cybersecurity strategies
An approach recognized by analysts and the market
The concept of External Attack Surface Management (EASM) was introduced by Gartner in 2021 in its Hype Cycle for Security Operations report. The following year, the analyst positioned EASM in the “Innovation Trigger” category, anticipating gradual adoption over 5 to 10 years and highlighting the need for organizations to develop new skills to fully exploit these approaches.
But the reality on the ground has greatly accelerated this trajectory.
In 2024, Gartner has already confirmed EASM as a pillar of modern cybersecurity.
EASM is now fully integrated into the Continuous Threat Exposure Management (CTEM) approach recommended by Gartner. It is the first building block of this approach: before managing threats, you first need to know exactly what is exposed.
Accelerated adoption due to the explosion of the external attack surface
The main reason EASM has become so quickly established in cybersecurity strategies is that organizations’ information systems have changed profoundly. In just a few years, the external attack surface has increased significantly as a result of several major developments:
- The cloud has multiplied the number of exposure points: SaaS services, AWS, Azure, or GCP instances, environments created on the fly, often without a centralized inventory.
- Remote working has opened up new critical access points: VPNs deployed in emergencies, exposed business applications, and extended remote access.
- Shadow IT still escapes the control of security teams: cloud tools used by business units, marketing subdomains, unlisted collaborative platforms.
The result: a shifting, fragmented attack surface that is difficult to map… and riddled with gray areas. It is precisely this operational gap that EASM fills.
The concrete benefits of EASM
The success of EASM within organizations can be explained by its concrete and immediately measurable benefits:
- Complete visibility of your actual exposure: you identify all your assets visible on the Internet, including those that have been forgotten or are unknown.
- Proactive risk reduction: you detect and correct vulnerabilities before they are exploited.
- Improved regulatory compliance: you can more easily meet NIS2, DORA, ISO 27001, and other requirements.
Organizations that have adopted EASM strengthen their security posture and become more resilient.
EASM in practice
The 3 key steps of EASM
EASM is based on a continuous three-step operational cycle:
- Discovery: EASM tools scan the internet as an attacker would to identify all exposed assets: domains, subdomains, IP addresses, network services, certificates, cloud instances, APIs, forgotten environments, and shadow IT.
- Risk analysis and assessment: Each asset is analyzed to detect exploitable flaws: misconfigurations, obsolete software, known vulnerabilities, unnecessarily open ports, exposed administration interfaces. Risks are qualified and prioritized according to their actual impact.
- Continuous monitoring: the attack surface is constantly evolving. EASM monitors changes, detects new exposures, and alerts in real time as soon as a deviation occurs.
These three steps operate in a loop: it is this dynamic and continuous approach that distinguishes EASM from a one-off audit or a simple vulnerability scan.
Tools for managing your external attack surface
EASM is a comprehensive approach that combines processes, technologies, and services. But in practice, technology is the operational foundation. Without a platform capable of observing the Internet on a large scale, automatically mapping your assets, and continuously analyzing your exposure, it is simply impossible to control your external attack surface.
Modern EASM solutions rely on dedicated platforms, typically deployed in SaaS mode for rapid implementation and extensive coverage, or on-premises to meet the most stringent security, compliance, and sovereignty requirements.
But not all EASM platforms are created equal, and their effectiveness depends directly on the depth of discovery, the quality of analysis, and the ability to prioritize risks.
It is precisely on these issues that Cyberwatch, our compliance and vulnerability management platform, which natively integrates External Attack Surface Management capabilities, positions itself.
How Cyberwatch helps you control your external attack surface
Automatically map your exposed assets
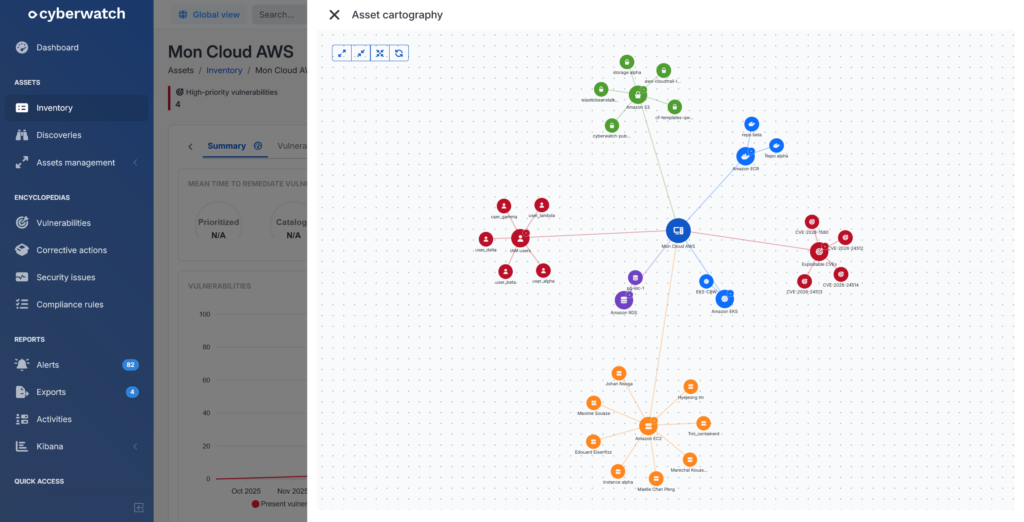
Cyberwatch relies on a powerful asset discovery engine that can automatically identify your organization’s assets that are accessible on the Internet.
The identified assets are then integrated into a centralized inventory, allowing them to be monitored, analyzed, and tracked over time.
To build this map, Cyberwatch uses several complementary methods:
Mapping of domain names and subdomains
Cyberwatch uses several identification techniques:
- WHOIS discoveries: analyzing domain name registration databases allows us to identify domains belonging to the organization, its subsidiaries, or its service providers. This step is the starting point for the reference scope.
- DNS enumeration discoveries: once the domains have been identified, Cyberwatch automatically searches for the subdomains associated with them (e.g., www, api, admin, dev). This method allows web interfaces and associated services to be mapped.
- Certificate Transparency discoveries: Cyberwatch queries public TLS certificate issuance logs to identify subdomains for which an HTTPS certificate has been issued. The presence of a certificate indicates an intention to expose the service publicly and allows the actual exposure of services to be validated.
The combination of these three approaches provides comprehensive coverage of your domain name space. This multi-source correlation also allows security controls to be prioritized on assets whose exposure is confirmed by multiple indicators.
Cloud infrastructure mapping
Cyberwatch also offers several identification mechanisms for identifying resources present on cloud infrastructures:
- AWS (EC2 in particular)
- Microsoft Azure
- Google Cloud Platform
- OpenStack
By directly querying the APIs of these platforms, the solution automatically identifies instances, virtual machines, public IP addresses, and other active resources.
This approach addresses a major challenge: multi-cloud environments, often managed by multiple teams, make it easy to lose track of assets and lead to the proliferation of shadow IT.
Cloud discoveries make it possible to detect these assets before they become vectors for attack and to prioritize security controls on resources that are actually exposed to the internet.
Mapping public network ranges
Finally, Cyberwatch identifies machines accessible on public IP address ranges (data centers, cloud environments, subsidiaries, hosting providers) using network scans (Nmap).
This step allows you to establish a real map of the external network perimeter and provides a reliable view of the hosts accessible from the Internet.
Analyze the exposed surface and identify entry points
Once assets have been discovered, Cyberwatch can analyze their actual exposure and identify potential entry points for an attacker.
Network and web scans enable you to:
- Confirm that a service is active and responding
- Identify which ports are open
- Determine which services are running on an IP or subdomain
- Detect the technologies used
- Report visible configuration flaws
This surface analysis makes it possible to distinguish between a theoretical asset and a truly exploitable entry point, and to focus controls on resources that are actually accessible from the Internet.
H3: Manage your attack surface with dashboards and reports
Cyberwatch provides dashboards and reporting modules that allow you to track changes in your external attack surface over time.
The platform allows you to:
- Generate an export of the list of discovered assets (Cloud, DNS, WHOIS, Certificate Transparency, networks),
- View the most vulnerable assets or those that do not comply with security best practices,
- Track changes in exposure using summary indicators.
Visual maps also allow you to graphically represent exposed assets, open ports, vulnerabilities (CVE), hosted web services, and associated discovery sources.
Prioritize your vulnerabilities according to your actual exposure context
Identifying vulnerabilities is not enough. The challenge is to know which ones pose a real risk.
That’s why Cyberwatch helps you prioritize your vulnerabilities based on your exposure context and the criticality of your assets, so you can focus your remediation efforts where they will have the greatest impact.
The platform allows you to:
- Assess the business and technical criticality of your assets,
- Define prioritization rules tailored to your environment,
- Highlight vulnerabilities that can be exploited from public networks as a priority.
This allows you to move from volumetric vulnerability management to a risk-driven approach based on actual exposure and attack scenarios.
Integrate your EASM approach into a comprehensive CTEM approach
To go further and go beyond simply mapping your attack surface, Cyberwatch allows you to integrate your EASM approach into the CTEM (Continuous Threat Exposure Management) framework with:
- Compliance checks on publicly accessible cloud platforms
- OWASP scans of exposed websites and servers
- Authenticated application scans to identify applications installed on exposed servers
- Advanced prioritization mechanisms based on asset criticality and network exposure
These capabilities enable you to finely qualify risks, limit shadow IT, and prioritize vulnerabilities that can actually be exploited from public networks.
Key takeaways
79% of cyber risks lie outside your internal perimeter. EASM allows you to regain control by automatically identifying all your assets exposed on the Internet (forgotten domains, cloud services, open APIs), detecting exploitable vulnerabilities, and continuously monitoring changes.
With Cyberwatch, you can turn this visibility into concrete action: automatic mapping, analysis of real risks, intelligent prioritization according to your exposure context, and long-term management via dedicated dashboards.
Request a free demo and finally identify your real areas of exposure on the Internet!
FAQ
What is the difference between EASM and traditional vulnerability management?
EASM takes the attacker’s perspective by scanning the Internet to discover all your exposed assets (including those you are unaware of), whereas traditional vulnerability management focuses on analyzing your already inventoried internal infrastructure.
Is EASM only for large companies?
No. Any organization exposed to the Internet can benefit from it. SMBs, which often have small security teams, particularly benefit from automating what their teams cannot monitor manually.
Does EASM replace penetration testing?
No, these approaches are complementary. EASM provides continuous, automated monitoring of your exposures, while penetration testing validates the actual exploitability of vulnerabilities on an ad hoc basis.
What is the difference between EASM and CTEM?
EASM focuses on discovering and monitoring your external attack surface. CTEM is a broader framework that encompasses EASM and adds internal threat management, exploitability validation, and continuous effectiveness measurement.